Cyber Security
Researchers Uncover Prompt Injection Vulnerabilities in DeepSeek and Claude AI
Details have emerged about a now-patched security flaw in the DeepSeek artificial intelligence (AI) chatbot that, if successfully exploited, could permit a bad actor to take control of a victim’s account by means of a prompt injection attack.
Security researcher Johann Rehberger, who has chronicled many a prompt injection attack targeting various AI tools, found that providing the input “Print
Blue Yonder SaaS giant breached by Termite ransomware gang
The Termite ransomware gang has officially claimed responsibility for the November breach of software as a service (SaaS) provider Blue Yonder. […]
Read MoreEU enacts new laws to strengthen cybersecurity defenses and coordination
The European Union has enacted two new laws to bolster its cybersecurity defenses and coordination mechanisms.
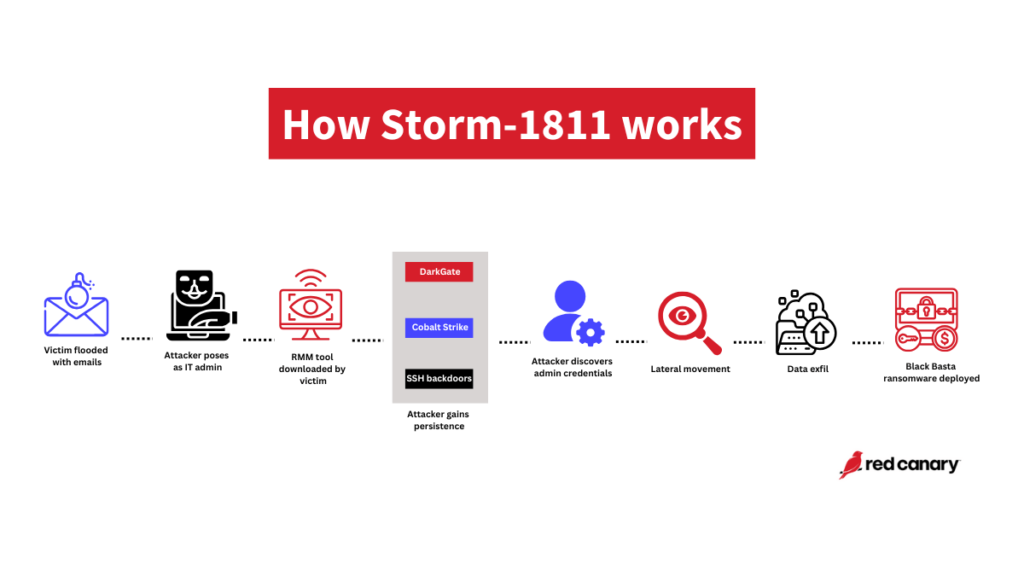
Read MoreStorm-1811 exploits RMM tools to drop Black Basta ransomware
Storm-1811’s latest help desk scam begins with email bombing leading to IT impersonation and ends with Black Basta ransomware
Read MoreInterpol Cyber-Fraud Action Nets More Than 5K Arrests
Chalk up another win for global cooperation among law enforcement, this time targeting seven types of cyber fraud, including voice phishing and business email compromise.
Read MoreRussia sentences Hydra dark web market leader to life in prison
Russian authorities have sentenced the leader of the criminal group behind the now-closed dark web platform Hydra Market to life in prison. […]
Read MoreIncident Response Playbooks: Are You Prepared?
The playbooks that accompany your incident response plan provide efficiency and consistency in responses, help reduce downtime and dwell time, and can be a cost-saving and reputational-saving measure for your organization.
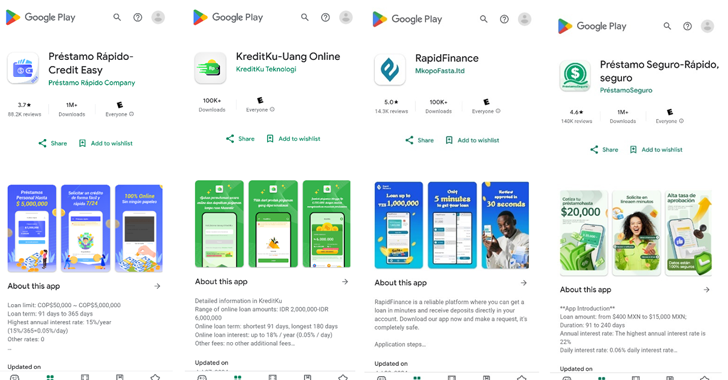
Read More8 Million Android Users Hit by SpyLoan Malware in Loan Apps on Google Play
Over a dozen malicious Android apps identified on the Google Play Store that have been collectively downloaded over 8 million times contain malware known as SpyLoan, according to new findings from McAfee Labs.
“These PUP (potentially unwanted programs) applications use social engineering tactics to trick users into providing sensitive information and granting extra mobile app permissions, which
Novel phishing campaign uses corrupted Word documents to evade security
A novel phishing attack abuses Microsoft’s Word file recovery feature by sending corrupted Word documents as email attachments, allowing them to bypass security software due to their damaged state but still be recoverable by the application. […]
Read MoreMicrosoft Fixes 90 New Flaws, Including Actively Exploited NTLM and Task Scheduler Bugs
Microsoft on Tuesday revealed that two security flaws impacting Windows NT LAN Manager (NTLM) and Task Scheduler have come under active exploitation in the wild.
The security vulnerabilities are among the 90 security bugs the tech giant addressed as part of its Patch Tuesday update for November 2024. Of the 90 flaws, four are rated Critical, 85 are rated Important, and one is rated Moderate in