Security News
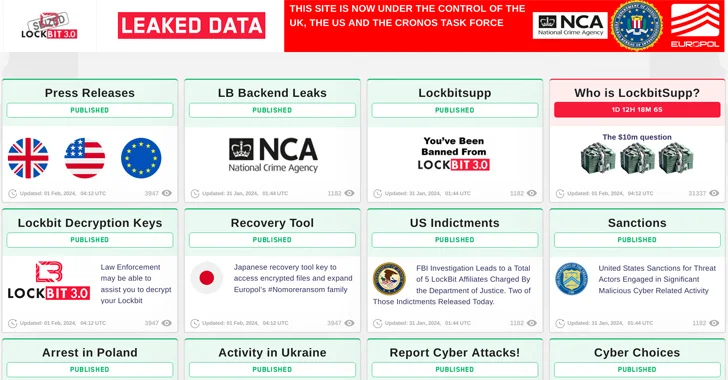
LockBit’s Leak Site Reemerges, a Week After ‘Complete Compromise’
Is LockBit dead? Law enforcement and the group itself seem to be telling conflicting stories.
Read MoreHijacked subdomains of major brands used in massive spam campaign
A massive ad fraud campaign named “SubdoMailing” is using over 8,000 legitimate internet domains and 13,000 subdomains to send up to five million emails per day to generate revenue through scams and malvertising. […]
Read MoreNorth Korean Hackers Targeting Developers with Malicious npm Packages
A set of fake npm packages discovered on the Node.js repository has been found to share ties with North Korean state-sponsored actors, new findings from Phylum show.
The packages are named execution-time-async, data-time-utils, login-time-utils, mongodb-connection-utils, and mongodb-execution-utils.
One of the packages in question, execution-time-async, masquerades as its legitimate
U.S. Offers $15 Million Bounty to Hunt Down LockBit Ransomware Leaders
The U.S. State Department has announced monetary rewards of up to $15 million for information that could lead to the identification of key leaders within the LockBit ransomware group and the arrest of any individual participating in the operation.
“Since January 2020, LockBit actors have executed over 2,000 attacks against victims in the United States, and around the world, causing costly
Police arrests LockBit ransomware members, release decryptor in global crackdown
Law enforcement arrested two operators of the LockBit ransomware gang in Poland and Ukraine, created a decryption tool to recover encrypted files for free, and seized over 200 crypto-wallets after hacking the cybercrime gang’s servers in an international crackdown operation. […]
Read MoreNew Report Reveals North Korean Hackers Targeting Defense Firms Worldwide
The North Korean state-sponsored threat actors have been attributed to a cyber espionage campaign targeting the defense sector across the world.
In a joint advisory published by Germany’s Federal Office for the Protection of the Constitution (BfV) and South Korea’s National Intelligence Service (NIS), the agencies said the goal of the attacks is to plunder advanced defense technologies in a “
Only 7% of Organizations Can Restore Data Processes within 1-3 Days After a Ransomware Attack
New data on how organizations are able to respond to ransomware attacks also shows that paying a ransom is highly likely, despite having a policy of “Do Not Pay.”
Read MoreCactus ransomware claim to steal 1.5TB of Schneider Electric data
The Cactus ransomware gang claims they stole 1.5TB of data from Schneider Electric after breaching the company’s network last month. […]
Read MoreAnatsa Android malware downloaded 150,000 times via Google Play
The Anatsa banking trojan has been targeting users in Europe by infecting Android devices through malware droppers hosted on Google Play. […]
Read MoreCritical Internet DNS flaw found by German Researchers
In a technical report, published by German researchers they demonstrate how with just a single DNS packet they can exhaust the DNS Server CPU and stall all widely-used DNS implementations and public DNS providers, such as Google Public DNS and Cloudflare. The impact of KeyTrap attacks is far-reaching. Exploiting KeyTrap, attackers can effectively disable Internet access in any system utilizing a DNSSEC-validating DNS resolver.
Read More